I decided to write a quick post on the topic as I just received one of these new scams and almost fell for it and hopefully can prevent someone else from falling for it. The scam campaign seems to be targeting small-medium sized businesses and may variate in tactics depending on the industry targeted, the email example below is real and should be used as a template for what to look out for.
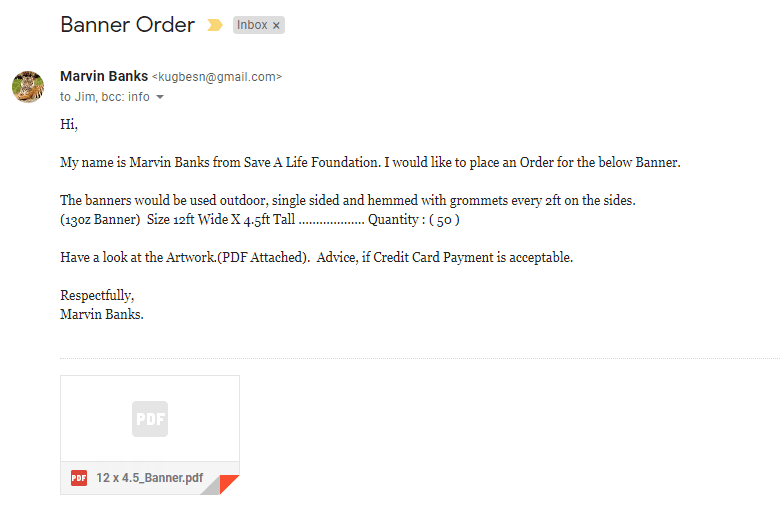
The prospect, in this case, is also the attacker (a fake prospect), sends a vague email as the one below (this is an actual scam email ):
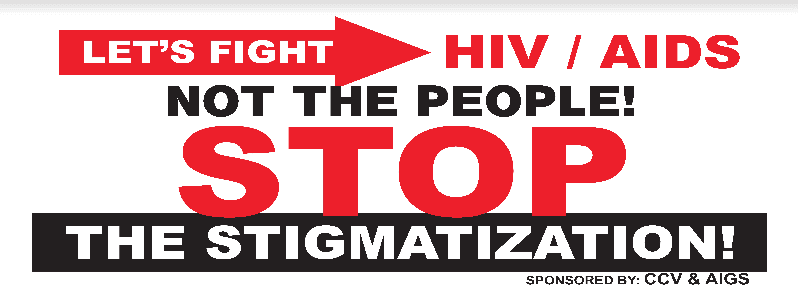
It Looks ok, right? Weary of the pdf attachment I scan it for malware or trojan but nothing was detected. I was still weary, being a computer & network security expert I decided to upload it to Google drive (lol) and previewed it there. To my surprise, it actually was a banner design…
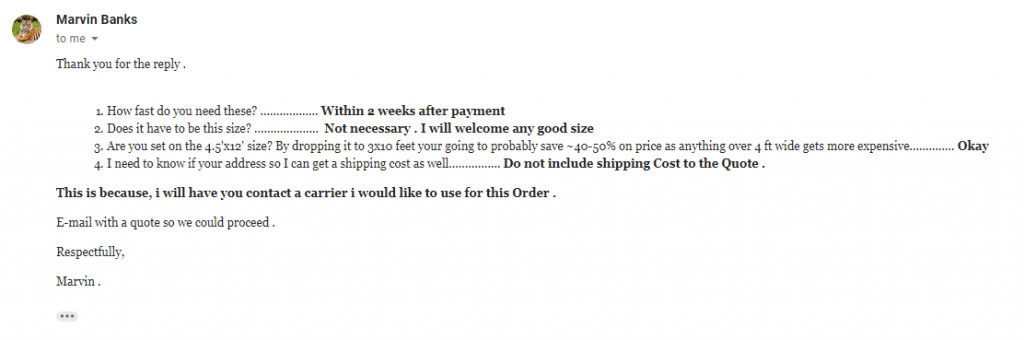
At this point, I was 75% convinced that this was a legitimate prospect. I decided to reply with additional questions required to effectively do the job or at least provide an accurate quote. The next day I received a reply:
After receiving the reply, I took some time to further analyze the entire conversation and began to find problems in his requests such as:
1. His email address, it was a Gmail address, easy to create anonymously.
2. Why is Save A Life Foundation (SALF) making banners for HIV/AIDS?
3. The banners mention sponsors but nothing about the SALF.
4. The banner size is an odd size, not a standard size, and doesn’t mind “any good” size.
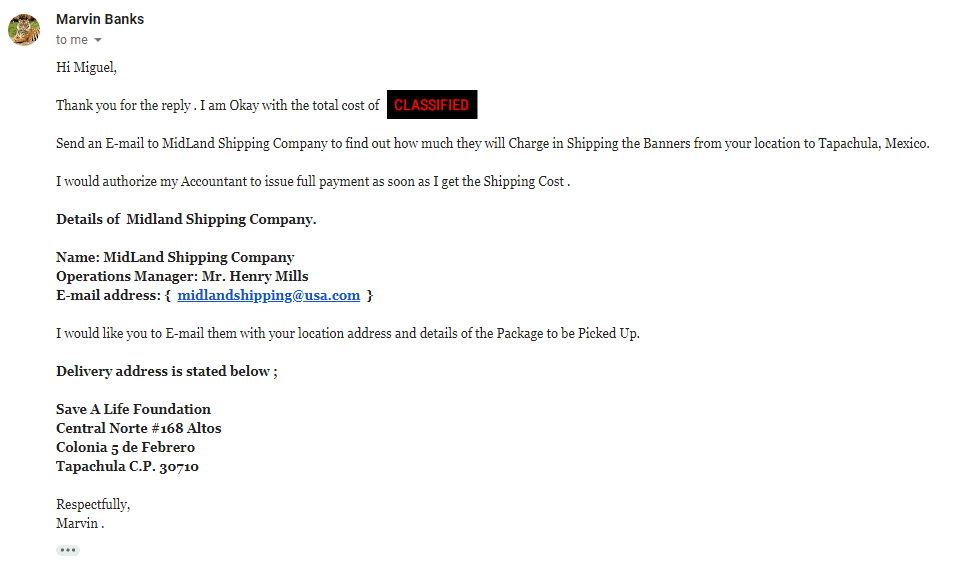
Still weary but curious, I decided to go further down the rabbit hole and give them a quote which they then replied:
After I received this response I was convinced it was a scam and decided to do some research.
So SALF is asking me to send banners to a Mexican Address huh? let’s check it out…
Yeah doesn’t look like the Save a Life Foundation unless they’ve downsized and are outsourcing now, it’s obviously not any organization saving lives.
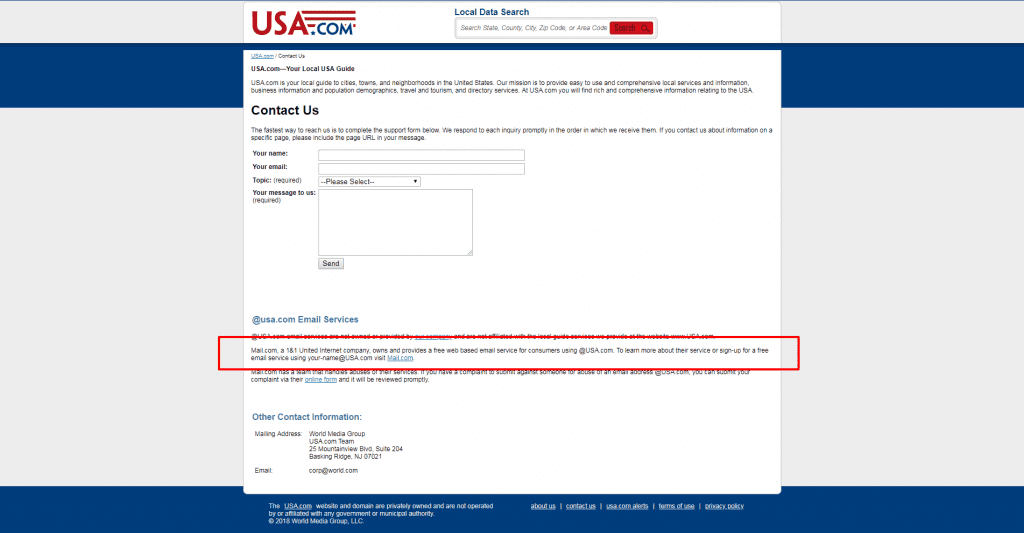
The email midlandshipping@usa.com looks absolutely wrong but somewhat legitimate because of the @usa.com domain behind it, which is why attacker used it. Thinking the attacker had compromised a mail server belonging to the domain, I decided to look at the domain in search for their abuse email so I could notify them of a possible breach with their mail server. Upon my search of the usa.com site, I came upon this on the usa.com site contact page.
So now we see how he was able to get the @usa.com email, it’s completely free.
This experience was annoying because of the time wasted but was good practice. I suggest people research companies who want to send your business requests for quotes and then ask to ship outside the country. Make sure their request makes logical sense, someone asking for something in quantity should be asking for standardized items and should require a standardized transactional process, no special or shady instructions, if it feels wrong don’t do it! In my case, it saved me a few thousand dollars that would have been most likely through a chargeback from a stolen credit card the attacker used.