This is another quick post to serve as a general note. This post will cover the install of PiHole with SSL on Apache. The guide should work for most Debian-based Linux distributions. We are running PHP7.4 as it’s native to the OS and does not require any PPA addons. You can install PHP8/+ if you like.
Step 1: Bash Into root
sudo bashEnter your password.
Step 2: Install Apache2
apt-get install apache2 -y
Step 3: Install PHP 7.4
apt-get install php -yapt-get install php-common php-mysql php-xml php-curl php-cli php-imap php-mbstring php-opcache php-soap php-zip php-intl php-sqlite3 -yStep 4: Install PiHole
curl -sSL https://install.pi-hole.net | bashDuring the course of the install, you will be prompted ~5 times. At the last prompt, you will be asked if you want to install the Lighttpd web server. At this point, you want to select no and complete the install process.
Once completed your PiHole setup should work. and should be accessible via ip/domain.com/admin/
Step 5 Cleanup:
As of today, I have noticed a rare glitch that will cause the folder structure to be odd after the pihole install. This can be easily fixed with the following details.
The default install will create folders like this:
pihole folder: /var/www/html/pihole
admin folder: /var/www/html/adminAlthough not a big deal, this causes a problem when trying to access the admin dashboard from the default pihole URL (http://ip/pihole), the link on the page that is supposed to link to the admin page will be broken. At this point, you can update the page link manually in pihole/index.php to forward to the correct URL or you can change/move folders to your liking.
To fix this issue, as root, first we move the folder to the correct directory.
mv /var/www/html/admin /var/www/html/piholeSecond, we update the default pihole root index file links
vim /var/www/www/html/pihole/index.php
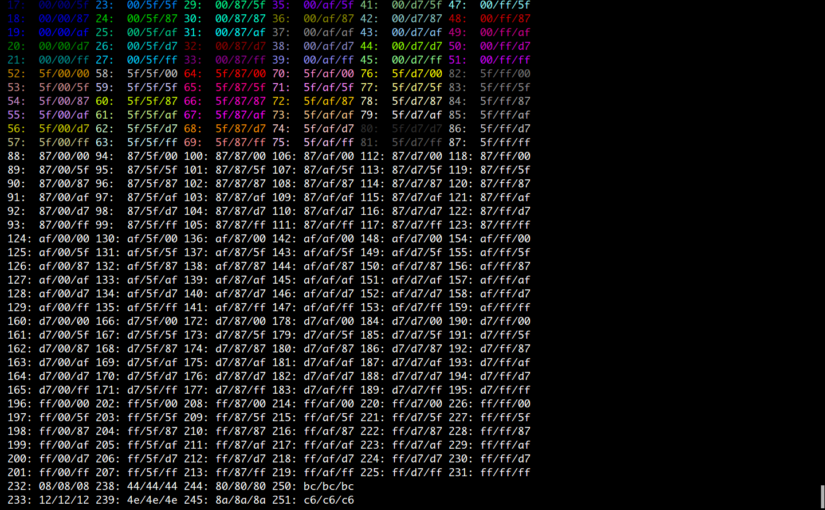
We want to edit three lines 77, 81, and 83 to reflect the new URL structure.
#Line 77:
<link rel='shortcut icon' href='/pihole/admin/img/favicons/favicon.ico' type='image/x-icon'>
#Line 81:
<img src='/pihole/admin/img/logo.svg' alt='Pi-hole logo' id="pihole_logo_splash">
#Line 83:
<a href='/pihole/admin/'>Did you mean to go to the admin panel?</a>Once done you can consider the process complete.
Step S: Installing SSL on PiHole:
To keep things classy, if not already, bash into root:
sudo bashLet’s enable the PHP’s SSL module and make our SSL folder to house our certs.
a2enmod sslmkdir /etc/apache2/certs/piholeNow let’s generate our self-signed cert:
openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/apache2/certs/pihole/piholio.key -out /etc/apache2/certs/pihole/piholio.crtEdit our default SSL virtual hosts config:
vim /etc/apache2/sites-available/default-ssl.confReplace lines 32 and 33 with the following lines
SSLCertificateFile /etc/apache2/certs/pihole/piholio.crt
SSLCertificateKeyFile /etc/apache2/certs/pihole/piholio.keySave and exit.
Next, enable SSL and restart the apache service:
a2ensite default-ssl.conf && systemctl restart apache2
At this point, you’ve successfully installed PiHole with SSL. We have another issue, by default apache does not reroute to SSL so you will still be able to visit the non-SSL URL. To fix this we need to enable the Rewrite module and enter our conditions into our domain’s virtual host configuration (or .htaccess).
Let’s enable that rewrite module:
a2enmod rewritesystemctl restart apache2Let’s edit our default virtual host file:
vim /etc/apache2/sites-available/000-default.confAdd the following three lines of code before the </VirtualHost> closing tag.
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule ^ https://%{SERVER_NAME}%{REQUEST_URI} [END,NE,R=permanent]Save the file and restart Apache.
systemctl restart apache2Your PiHole install should now be “running in SSL”. If anyone viewing my notes has questions feel free to leave a comment.